VMware Horizon View 5.2 Feature Pack 1: Web Access & Utility Touch
With the release of VMware Horizon View 5.2, comes the Feature Pack 1 which allows Web Access through browsers and as well as Touch Utility found on Horizon View mobile client on Android and Apple. You can view all these nice features from my previous post on Horizon Suite.
Today I will summarize some of the requirements to get the Feature Pack 1 installed. I would not go into much details as the documentation provided on Horizon View are sufficient to do any simple installation and as my previous post there reviewer's guide provide a very detailed step by step which you can refer to.
Please note that HTML Access is only enabled for all PC and Mac specific browsers supporting HTML5. iPad running iOS6 or higher with Safari is also possible however if your iPad is installed with mobile Horizon View Client, the default action is to use the Horizon View Client instead unless it is not available
Also HTML Access has only image projection, there is no audio. Functions and features e.g. USB redirection and audio requires the use of Horizon View Client.
To know the end points supported with which browsers, please refer to this document.
To get Feature Pack 1 working, you would need the below:
As mentioned on Step 4 above, you will see the option as show below:
If you did not enable this checkbox, you will only be able to access the Desktop via the client but not via HTML.
Step 5, three inbound Windows firewall rules greyed out showing its disabled. You would just need to enable it on the Security Server. It is recommended to check that the Connection Server has the inbound rules enabled as well. You will realize the description is "Blast-in".
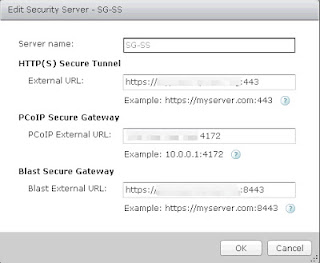
Step 6, You find a new Blast External URL gateway for both on Connection and Security Server.
A view of Utility touch on my Samsung Note II mobile phone allows the ease of using Windows and access the Start Menu more efficiently. Do note that Utility Touch is only supported on mobile Horizon View Client for Apple and Android.
There is also included policy which can use to configure some parameters for Blast. You can see from the screenshot below. Import just like View policy for persona and PCoIP.
At the time of writing, I have tested the HTML Access using Windows 7 to work successfully. Windows XP seems to have some issues and encounter this error message when using HTML Access
On a side note learned from my Home Lab
I set this up in my Home Lab and have used all the internal IP and FQDN for the Connection Server External URL and IP and for the Security Server, I have used the public IP and DNS.
I was able to perform all client access however I encounter HTML access from WAN failed with timeout after selecting a desktop via the Security Server. I know the connection to Connection Server was successful because I was provided with the front facing page of HTML Access since that package is installed only on Connection Server.
I have directed 443, 4172 and 8443 to my Security Server which is facing my router which is internet facing. After analyzing again, your internal network which is your Connection Server must be able to recognize the external URL/IP of the Security Server. This is something which my internal network gateway is unable to resolve. I added another gateway which is public DNS aware and this resolve.
What was learned from this is that 8443 need to be dual directional. Meaning that Security Server will pass the traffic to Connection Server who will redirect this back to Security Server. Connection Server must be able to resolve the External URL of the Security Server.
Today I will summarize some of the requirements to get the Feature Pack 1 installed. I would not go into much details as the documentation provided on Horizon View are sufficient to do any simple installation and as my previous post there reviewer's guide provide a very detailed step by step which you can refer to.
Please note that HTML Access is only enabled for all PC and Mac specific browsers supporting HTML5. iPad running iOS6 or higher with Safari is also possible however if your iPad is installed with mobile Horizon View Client, the default action is to use the Horizon View Client instead unless it is not available
Also HTML Access has only image projection, there is no audio. Functions and features e.g. USB redirection and audio requires the use of Horizon View Client.
To know the end points supported with which browsers, please refer to this document.
To get Feature Pack 1 working, you would need the below:
- Horizon View 5.2 (You need to be at this version)
- Install Feature Pack 1 HTML Access on Horizon View Connection Servers
- Feature Pack 1 agent to be installed on all master VM/Desktop used in desktop pools
- Enable HTML Access in Desktop Pools settings
- Enable Inbound Windows Firewall rules 8443 on Security Server (which is precreated when you install Security Server 5.2)
- Edit Blast Secure Gateway on both Connection and Security Server if it differs from what is entered by default during installation
As mentioned on Step 4 above, you will see the option as show below:
If you did not enable this checkbox, you will only be able to access the Desktop via the client but not via HTML.
Step 5, three inbound Windows firewall rules greyed out showing its disabled. You would just need to enable it on the Security Server. It is recommended to check that the Connection Server has the inbound rules enabled as well. You will realize the description is "Blast-in".
Step 6, You find a new Blast External URL gateway for both on Connection and Security Server.
A view of Utility touch on my Samsung Note II mobile phone allows the ease of using Windows and access the Start Menu more efficiently. Do note that Utility Touch is only supported on mobile Horizon View Client for Apple and Android.
Utility Touch on Windows XP
Utility Touch on Windows 7
There is also included policy which can use to configure some parameters for Blast. You can see from the screenshot below. Import just like View policy for persona and PCoIP.
At the time of writing, I have tested the HTML Access using Windows 7 to work successfully. Windows XP seems to have some issues and encounter this error message when using HTML Access
An error has occurred: {"code":"ECONNRESET"}
On a side note learned from my Home Lab
I set this up in my Home Lab and have used all the internal IP and FQDN for the Connection Server External URL and IP and for the Security Server, I have used the public IP and DNS.
I was able to perform all client access however I encounter HTML access from WAN failed with timeout after selecting a desktop via the Security Server. I know the connection to Connection Server was successful because I was provided with the front facing page of HTML Access since that package is installed only on Connection Server.
I have directed 443, 4172 and 8443 to my Security Server which is facing my router which is internet facing. After analyzing again, your internal network which is your Connection Server must be able to recognize the external URL/IP of the Security Server. This is something which my internal network gateway is unable to resolve. I added another gateway which is public DNS aware and this resolve.
What was learned from this is that 8443 need to be dual directional. Meaning that Security Server will pass the traffic to Connection Server who will redirect this back to Security Server. Connection Server must be able to resolve the External URL of the Security Server.






Comments
I'm testing HTML Access and i've the same problema. I think that is a configuration firewall problem because Vmware Blast requires that Firewall will be enabled.
If you have any news please comment them with us.
PD: I like your blog from now i'm going to follow it.
Regards